IP-MAC Lock Switch
․ 24 RJ-45 10/100Base-T ports
․2 Gigabit 1000 Base port
Supports:
IP/ MAC / Port / VLAN Auto Learning
Qualityof Service
․L2/L3/L4Traffic Castigation/ Priority Management
․Cos(Class of Service) by IEEE802.1 p4 priority queues control
Performance
․MAC address:8K
․Physical address can be sat automatically or manually
L2Features
․IP-MAC-Port-VLAN Lock Rule:200
․Full-duplex mode on port 25 and 26 when working the Gigabit speed
․Port Mirroring: Supports Mirror function per port
․Spanning Tree: Supports 802.1d STP,802.1w RSTP
․Broadcast storm control
․Supports VLAN
․Support IEEE802.1Q VLAN
․Support Tag
․Support unTag VLAN
․Support LLDP
ProvidesLink Aggregation
․Support Up to 8 port in one trunk
․Up to 13 trunk group
․Support 802.3ad (LACP)
IPManagement IEEEStandards
․DHCP server ․ IEEE802.3
․Support Static IP ․ IEEE802.3u
Event/Error Log Management․ IEEE802.3z
․ Supports Dump Log ․ IEEE802.3x(Full-duplex flow control)
ManagementMechanical
RMON․ Dimensions:258mm x 444mm x 44mm
․ Supports MIBII(19�� rack mount standard)
․ Supports RMON MIB․ LED indicators : Port, Uplink, System,
․ Supports Bring MIB Stack/ Master
․ Supports Private MIB․ Weight: 3.3KG
ManagementSystem ElectromagneticCompatibility
․ Supports SNMP․ CE Mark
FirmwareUpgrade ․ FCC Class A
․ Provides TFTP RoHS
MaintenancePowerRequirement
․ Provides backup ․ Normal Input Voltages: 100-240 V
․ Provides recovery ․ Input Frequency: 47-63Hz
I/OPorts
․24 RJ-45 10/100 Base-T ports
․ RS-232c
․ DB-9 Console Port
․ 1000 base- SX or 1000 base LX, or 1000 base-T
․ MDI/ MID-X
․ Supports auto judgment per port
About IP-MAC Lock Switch Special function
Adopt the latest ASIC chip, handle effect doubly
The complete hardware type handles the function of IP- MAC Lock.
Support Chinese and English two kinds of management interfaces
Founding exchanger Chinese turns management interface, managing more diversified.
Learn on-line IP/ MAC/ Port/ VLAN information automatically
Don't need to pursue a pen to key-in IP/ MAC data, can be opened by automatic lieutenant general legal user of the learning detailed list to allow detailed list.
Can the single wharf choose the IP �V MAC Lock or Mapping function
Information personnel's going to work time can choose Lock function, the public holiday can start Mapping function, let lightly loose loosen management network!
The bandwidth limits
Accurate bandwidth restriction, minimum limit unit: 64 kbps.
Layer 2 ~ Layer 4 ACL
The whole hardware type ACL controls.
VLAN advantage
Support 4094 sets of VLANs, can set 4094 sets of VLANs once.
DHCP Client
Can aim at a fixed wharf the DHCP function of the start static state, the user can obtain same
IP every time through the DHCP function.
DHCP Server Filter
Can expel other illegal DHCP Servers to equip, avoid IP issue's conflict influencing a network
to use normally.
Have a distant place management function
The IP canned carry on a distant place management through the Web method, and canned limit ten sets of particular IP on-line a management, been not allowed can't on-line.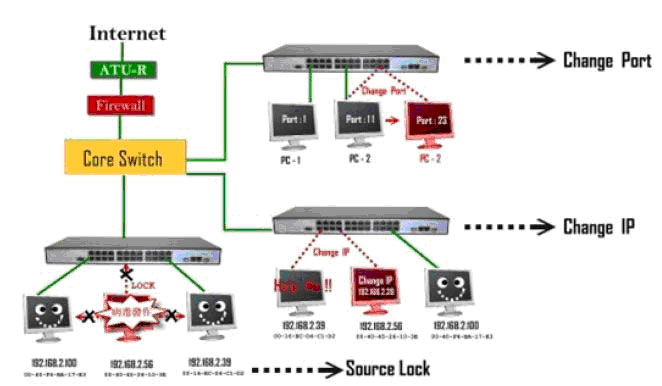
When the User Changes IP:
The AAFSG-2242 can lock him, even change to return to correct IP still can't on-line , having to
be relieved by the MIS personnel to target just can recover an on-line.
When the User Changes MAC:
The AAFSGG-2242 can lock him, even change to return to correct MAC still can't on-line, having to be relieved by the MIS personnel to target just can recover an on-line.
When the User Changes Link Port :
The AAFSG-2242 can lock him , even change to return to correct Link Port still can't on-line, having to be relieved by the MIS personnel to target just can recover an on-line.
About Source Lock
When act against the user of policy is locked by the AAFSG-2242, one of his discharge is to can't carry other users through the AAFSG-2242 influence LAN
Other switches can only lock destination, Only AAFSG-2242 can lock source to carry.

When the Content SQR runs into IP-MAC Lock Control
It is provided Email, WebMail, Web, IM, P2 P, FTP by the Content SQR..Wait for an application layer auditor management with safe content, in addition to blockading a dangerous
communication content, match again target function after stopping network on-line and then can loosen to guard against lightly up the IP-MAC Lock Control not appropriate usage network resource, reduce loss risk.
Above diagram is example:
B3 users find after detecting filter through the Content SQR user in addition to discharge abnormality, the WebMail still clips to bring the company important information to deliver to
other places, violating the rules in really and seriously behavior, the SQR of the Content will will violate the rules to record notice Control Server at this time, after descend to attain blockader instruction the Lock Control is to the IP-MAC, the IP of B3:192.168.5.13 Locks(the lock live), immediately and compulsory stop usage network, reach directly commanding defensive management.

Auto-adaptive IP-MAC control
Found to brush a card control IP a start exclusively, make use of the IP-MAC Lock Control
function, control IP usage appearance strictly, the not afraid network permits phenomenon easily
any further, observant and conscientious person private again how imitate a legality, the status still keeps escaping however the IP-MAC Lock Control of tight control, ignore is be on business, ask
for leave to still keep going off work, don't enter office not to brush to go through card, the IP is locked forever of, any ones all can't steal!
Lock function most the Jing is tight to control with the usage, don't need to worry IP or MAC to be copied, a thin card makes the office more safe.
This function needs to match appropriation to brush card machine, can choose card to respond, the fingerprint respond, the lines of the palm respond and the vein detect.
This series function the patent application is medium currently.

All Control
Place the IP-MAC Lock Switch to carry in the network limit, all computer users can accept
the IP-MAC Lock Control to control directly, can set the user as the IP-MAC Lock by port, in addition to direct restriction the user change IP or MAC to set, can also limit an usage of
linking the wharf, once when the user changes conjunction wharf without authorization, the
IP-MAC Lock Control function will will violate the rules immediately the lock live.
When certain user suffers the IP-MAC Lock Control, the function locks compulsory, that
user's sealing to wrap is to can't pass the IP-MAC lock Switch to then influence other users,
this series product's lying in the target for targeting with other Switches' biggest dissimilarities
is a source to carry(Source), not destination(Disconnection), so can insure LAN of clean empty.
This type configures a fit demand to control the unit usage of user strictly.
․IP-MAC exchange transmission rate up to 9.6 Gbps
Memory
․ Packet buffering:32 Mbps
․ Supports store and forward
Management
․ Supports Telnet
․ Supports SSH
․ Supports remote control function
․SNMP V1/V2c/V3
․ RS-232 Local Console setting Cisco Like(CLI)
․ Web management interface










